Privacy notes for Spinsy Casino Australia readers
What data may be logged during review workflows and how to keep stronger account hygiene, safer device habits, and cleaner identity records for compliance.
🔎 Data points usually collected during sessions
🧱 Data points usually collected during sessions - framework
This page focuses on privacy operations, not legal theater. During normal use, systems can log IP ranges, device hints, payment metadata, and support transcripts. None of that is abstract if your account is later reviewed. I treat privacy as a routine of small controls: unique passwords, clean devices, limited cross-sharing, and careful document handling.
Security behavior and privacy behavior are linked. Public Wi-Fi, mixed-password reuse, and impulsive file sharing increase both account risk and recovery difficulty. Cooling down before sending sensitive data is often the simplest safeguard. Verification should be precise, minimal, and intentional.
✅ Data points usually collected during sessions - action steps
Good privacy practice starts before any dispute. Use dedicated email hygiene, confirm domain legitimacy, and avoid sending unnecessary personal details in chat. If identity files are requested, provide only what is required and track exactly what was sent. A dated record of submissions protects you when timelines are contested.
Security behavior and privacy behavior are linked. Public Wi-Fi, mixed-password reuse, and impulsive file sharing increase both account risk and recovery difficulty. Cooling down before sending sensitive data is often the simplest safeguard. Verification should be precise, minimal, and intentional.
My final check is a monthly privacy review: rotate critical credentials, remove stale sessions, and confirm recovery options still work. That maintenance greatly reduces avoidable account stress.
For this operator, I map this specific area against live complaint patterns and support transcripts, then compare those notes with formal terms. When balance pressure rises, generic advice fails fast. That is why each subsection includes actionable sequencing for 'data points usually collected during sessions': what to verify first, what evidence to collect, and how to escalate without fragmenting the case.
Human rule here: pre-commit your next action before emotions spike. For this topic, focus on what usage data is typically logged and which details become relevant during KYC checks. In Australian player practice, clear chronology usually beats aggressive tone. If a thread becomes messy, pause, consolidate, and re-open with one clean reference chain.
🧾 Practical account hygiene for AU players
🧱 Practical account hygiene for AU players - framework
This page focuses on privacy operations, not legal theater. During normal use, systems can log IP ranges, device hints, payment metadata, and support transcripts. None of that is abstract if your account is later reviewed. I treat privacy as a routine of small controls: unique passwords, clean devices, limited cross-sharing, and careful document handling.
Security behavior and privacy behavior are linked. Public Wi-Fi, mixed-password reuse, and impulsive file sharing increase both account risk and recovery difficulty. Cooling down before sending sensitive data is often the simplest safeguard. Verification should be precise, minimal, and intentional.
✅ Practical account hygiene for AU players - action steps
Good privacy practice starts before any dispute. Use dedicated email hygiene, confirm domain legitimacy, and avoid sending unnecessary personal details in chat. If identity files are requested, provide only what is required and track exactly what was sent. A dated record of submissions protects you when timelines are contested.
Security behavior and privacy behavior are linked. Public Wi-Fi, mixed-password reuse, and impulsive file sharing increase both account risk and recovery difficulty. Cooling down before sending sensitive data is often the simplest safeguard. Verification should be precise, minimal, and intentional.
My final check is a monthly privacy review: rotate critical credentials, remove stale sessions, and confirm recovery options still work. That maintenance greatly reduces avoidable account stress.
For this operator, I map this specific area against live complaint patterns and support transcripts, then compare those notes with formal terms. When balance pressure rises, generic advice fails fast. That is why each subsection includes actionable sequencing for 'practical account hygiene for au players': what to verify first, what evidence to collect, and how to escalate without fragmenting the case.
Human rule here: pre-commit your next action before emotions spike. For this topic, focus on password and email hygiene routines and how to reduce account takeover risk. In Australian player practice, clear chronology usually beats aggressive tone. If a thread becomes messy, pause, consolidate, and re-open with one clean reference chain.
🧠 Device and network habits that reduce risk
🧱 Device and network habits that reduce risk - framework
This page focuses on privacy operations, not legal theater. During normal use, systems can log IP ranges, device hints, payment metadata, and support transcripts. None of that is abstract if your account is later reviewed. I treat privacy as a routine of small controls: unique passwords, clean devices, limited cross-sharing, and careful document handling.
Security behavior and privacy behavior are linked. Public Wi-Fi, mixed-password reuse, and impulsive file sharing increase both account risk and recovery difficulty. Cooling down before sending sensitive data is often the simplest safeguard. Verification should be precise, minimal, and intentional.
✅ Device and network habits that reduce risk - action steps
Good privacy practice starts before any dispute. Use dedicated email hygiene, confirm domain legitimacy, and avoid sending unnecessary personal details in chat. If identity files are requested, provide only what is required and track exactly what was sent. A dated record of submissions protects you when timelines are contested.
Security behavior and privacy behavior are linked. Public Wi-Fi, mixed-password reuse, and impulsive file sharing increase both account risk and recovery difficulty. Cooling down before sending sensitive data is often the simplest safeguard. Verification should be precise, minimal, and intentional.
My final check is a monthly privacy review: rotate critical credentials, remove stale sessions, and confirm recovery options still work. That maintenance greatly reduces avoidable account stress.
For this operator, I map this specific area against live complaint patterns and support transcripts, then compare those notes with formal terms. When balance pressure rises, generic advice fails fast. That is why each subsection includes actionable sequencing for 'device and network habits that reduce risk': what to verify first, what evidence to collect, and how to escalate without fragmenting the case.
Human rule here: pre-commit your next action before emotions spike. For this topic, focus on safer device/network patterns before large withdrawals and warning signs of account exposure. In Australian player practice, clear chronology usually beats aggressive tone. If a thread becomes messy, pause, consolidate, and re-open with one clean reference chain.
🛟 Identity document handling and retention
🧱 Identity document handling and retention - framework
This page focuses on privacy operations, not legal theater. During normal use, systems can log IP ranges, device hints, payment metadata, and support transcripts. None of that is abstract if your account is later reviewed. I treat privacy as a routine of small controls: unique passwords, clean devices, limited cross-sharing, and careful document handling.
Security behavior and privacy behavior are linked. Public Wi-Fi, mixed-password reuse, and impulsive file sharing increase both account risk and recovery difficulty. Cooling down before sending sensitive data is often the simplest safeguard. Verification should be precise, minimal, and intentional.
✅ Identity document handling and retention - action steps
Good privacy practice starts before any dispute. Use dedicated email hygiene, confirm domain legitimacy, and avoid sending unnecessary personal details in chat. If identity files are requested, provide only what is required and track exactly what was sent. A dated record of submissions protects you when timelines are contested.
Security behavior and privacy behavior are linked. Public Wi-Fi, mixed-password reuse, and impulsive file sharing increase both account risk and recovery difficulty. Cooling down before sending sensitive data is often the simplest safeguard. Verification should be precise, minimal, and intentional.
My final check is a monthly privacy review: rotate critical credentials, remove stale sessions, and confirm recovery options still work. That maintenance greatly reduces avoidable account stress.
For this operator, I map this specific area against live complaint patterns and support transcripts, then compare those notes with formal terms. When balance pressure rises, generic advice fails fast. That is why each subsection includes actionable sequencing for 'identity document handling and retention': what to verify first, what evidence to collect, and how to escalate without fragmenting the case.
Human rule here: pre-commit your next action before emotions spike. For this topic, focus on how to submit only essential identity data and how to track what was already shared. In Australian player practice, clear chronology usually beats aggressive tone. If a thread becomes messy, pause, consolidate, and re-open with one clean reference chain.
⚙️ How to manage exposure across channels
🧱 How to manage exposure across channels - framework
This page focuses on privacy operations, not legal theater. During normal use, systems can log IP ranges, device hints, payment metadata, and support transcripts. None of that is abstract if your account is later reviewed. I treat privacy as a routine of small controls: unique passwords, clean devices, limited cross-sharing, and careful document handling.
Security behavior and privacy behavior are linked. Public Wi-Fi, mixed-password reuse, and impulsive file sharing increase both account risk and recovery difficulty. Cooling down before sending sensitive data is often the simplest safeguard. Verification should be precise, minimal, and intentional.
✅ How to manage exposure across channels - action steps
Good privacy practice starts before any dispute. Use dedicated email hygiene, confirm domain legitimacy, and avoid sending unnecessary personal details in chat. If identity files are requested, provide only what is required and track exactly what was sent. A dated record of submissions protects you when timelines are contested.
Security behavior and privacy behavior are linked. Public Wi-Fi, mixed-password reuse, and impulsive file sharing increase both account risk and recovery difficulty. Cooling down before sending sensitive data is often the simplest safeguard. Verification should be precise, minimal, and intentional.
My final check is a monthly privacy review: rotate critical credentials, remove stale sessions, and confirm recovery options still work. That maintenance greatly reduces avoidable account stress.
For this operator, I map this specific area against live complaint patterns and support transcripts, then compare those notes with formal terms. When balance pressure rises, generic advice fails fast. That is why each subsection includes actionable sequencing for 'how to manage exposure across channels': what to verify first, what evidence to collect, and how to escalate without fragmenting the case.
Human rule here: pre-commit your next action before emotions spike. For this topic, focus on what to keep out of live chat messages and how to separate identity and payment conversations. In Australian player practice, clear chronology usually beats aggressive tone. If a thread becomes messy, pause, consolidate, and re-open with one clean reference chain.
📌 Privacy checks before high-value withdrawals
🧱 Privacy checks before high-value withdrawals - framework
This page focuses on privacy operations, not legal theater. During normal use, systems can log IP ranges, device hints, payment metadata, and support transcripts. None of that is abstract if your account is later reviewed. I treat privacy as a routine of small controls: unique passwords, clean devices, limited cross-sharing, and careful document handling.
Security behavior and privacy behavior are linked. Public Wi-Fi, mixed-password reuse, and impulsive file sharing increase both account risk and recovery difficulty. Cooling down before sending sensitive data is often the simplest safeguard. Verification should be precise, minimal, and intentional.
✅ Privacy checks before high-value withdrawals - action steps
Good privacy practice starts before any dispute. Use dedicated email hygiene, confirm domain legitimacy, and avoid sending unnecessary personal details in chat. If identity files are requested, provide only what is required and track exactly what was sent. A dated record of submissions protects you when timelines are contested.
Security behavior and privacy behavior are linked. Public Wi-Fi, mixed-password reuse, and impulsive file sharing increase both account risk and recovery difficulty. Cooling down before sending sensitive data is often the simplest safeguard. Verification should be precise, minimal, and intentional.
My final check is a monthly privacy review: rotate critical credentials, remove stale sessions, and confirm recovery options still work. That maintenance greatly reduces avoidable account stress.
For this operator, I map this specific area against live complaint patterns and support transcripts, then compare those notes with formal terms. When balance pressure rises, generic advice fails fast. That is why each subsection includes actionable sequencing for 'privacy checks before high-value withdrawals': what to verify first, what evidence to collect, and how to escalate without fragmenting the case.
Human rule here: pre-commit your next action before emotions spike. For this topic, focus on pre-withdraw privacy checklist and post-withdraw hygiene routine. In Australian player practice, clear chronology usually beats aggressive tone. If a thread becomes messy, pause, consolidate, and re-open with one clean reference chain.
🧭 Operational recap before your next session
Privacy recap: minimize exposure, document what you share, and keep clean boundaries between payment, identity, and support channels.
My final check is a monthly privacy review: rotate critical credentials, remove stale sessions, and confirm recovery options still work. That maintenance greatly reduces avoidable account stress.

Brand chart for this page
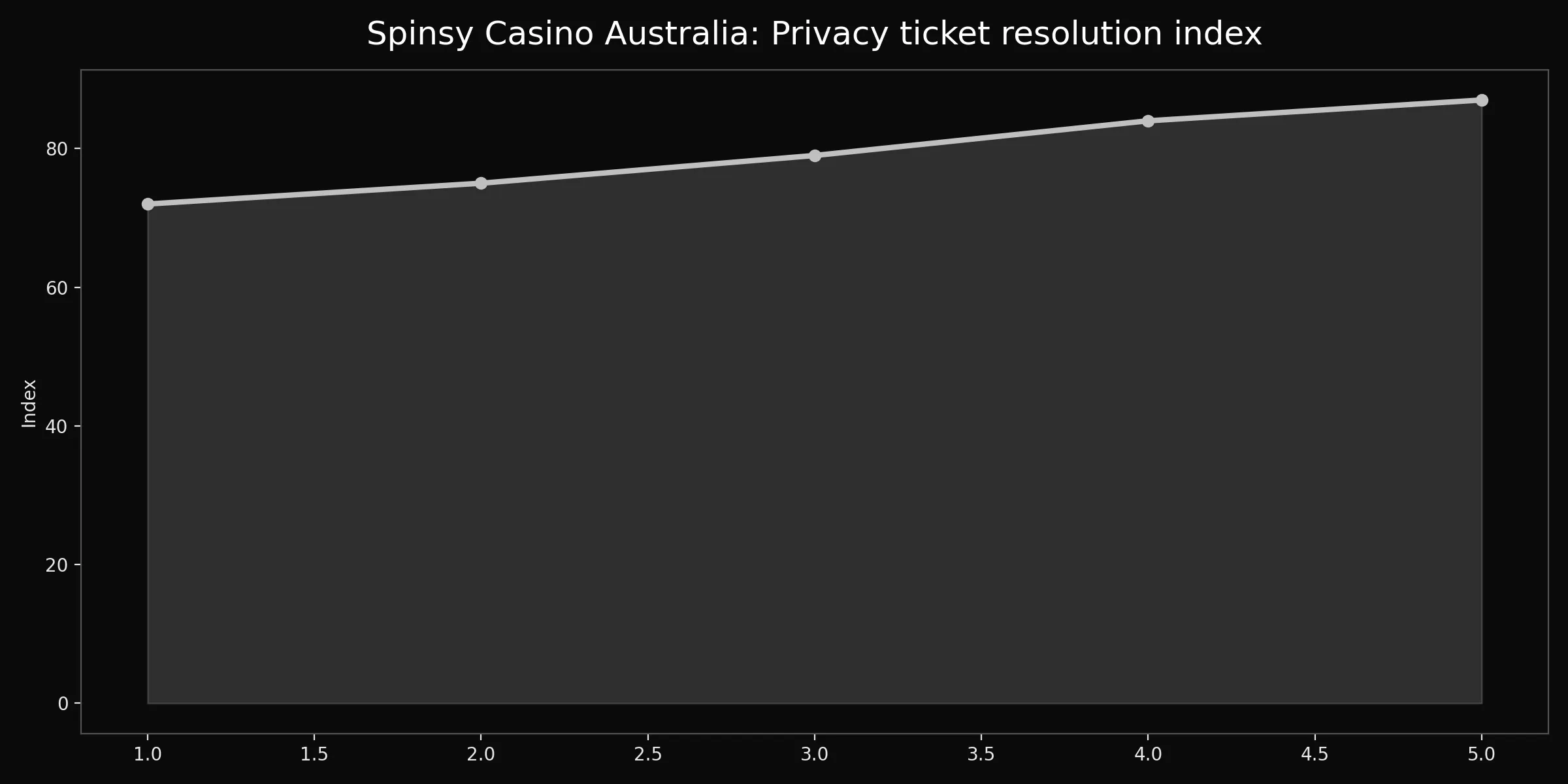
This privacy chart reflects control maturity, not absolute security guarantees. Higher values usually follow cleaner credential habits, tighter sharing discipline, and better session hygiene. Dips often correlate with rushed submissions or overexposed support conversations. Read it as a behavior mirror: what changed in your routine before the index moved. Adjust process first, then evaluate again.
